HIPAA Compliance Checklist for 2025

Keeping sensitive data secure becomes increasingly complex as organizations grow. With expanding teams, third-party vendors, and remote work setups, managing access to critical resources can quickly turn into a security risk.
The challenge?
Ensuring the right people have access to the right information - no more, no less.
Role-Based Access Control (RBAC) provides a solution by granting permissions based on specific job roles, making it easier to safeguard data without micromanaging every user’s access.
But how does it help with keeping your data secure?
Here in the article, we will explore how RBAC works, its key benefits, and the best practices for setting up a secure, scalable access control system that aligns with today’s dynamic IT environments.
TL;DR
- Role-based access control (RBAC) assigns access based on job roles, ensuring employees only access information necessary for their responsibilities reducing data breach risks.
- Key RBAC components include roles, permissions, users, and constraints, with models like core, hierarchical, and constrained RBAC for flexibility.
- Implementing RBAC enhances data protection, simplifies compliance, and streamlines permissions management, saving time and resources.
- Common challenges like role explosion and over-permissions can be managed through regular audits and best practices.
- CloudEagle.ai automates RBAC across SaaS tools, enabling centralized control, automated provisioning, and compliance tracking for efficient access management.
1. RBAC Explained: Who Can See What and Why?
Role-Based Access Control (RBAC) manages IT resource access by assigning permissions to specific roles rather than individuals. This approach adheres to the least privilege principle, ensuring users only access the data necessary for their job functions.
- Simplified Governance: RBAC optimizes access management in large organizations by aligning permissions with responsibilities.
- Operational Efficiency: Using predefined roles like Administrator or Data Analyst minimizes human error and allows for quick access adjustments during personnel changes.
- Reduced Security Risks: By limiting over-privileged accounts, it effectively protects sensitive enterprise data.
A. What Are the Three Types of RBAC?
RBAC systems can vary in complexity, depending on the organization’s needs. Here are the types of access control:
- Core RBAC: The simplest role based access control model, where each user is tied to one or more predefined roles.
- Hierarchical RBAC: In this model, roles inherit permissions from other roles, ideal for layered organizational structures.
- Constrained RBAC: Adds limits through separation of duties, reducing the risk of conflict or fraud.
B. What Are the Disadvantages of RBAC?
While RBAC offers many benefits, it has a few limitations:
- Role Explosion: Too many narrowly defined roles can make the system hard to manage.
- Maintenance Overhead: As organizations grow, updating roles and policies frequently becomes essential.
Inflexibility in Dynamic Environments: RBAC works well in stable roles but may struggle in agile or cross-functional setups without proper role reviews.
2. How RBAC Actually Works Behind the Scenes?
To understand how RBAC strengthens security, let’s break down its core components. Each component plays a critical role in defining, managing, and controlling access permissions across an organization:
- Roles: In RBAC, a role represents a set of permissions assigned based on job responsibilities. For example, an “Administrator” role might have permissions to manage user accounts and sensitive data, while an “Employee” role may only access essential applications and documents.
- Permissions: Permissions define what actions a user in a specific role can perform. Each role can contain permissions like “view only,” “edit,” or “delete, ”depending on the level of access required.
- Users: Users get the roles that match their responsibilities. Organizations streamline access control by aligning users with roles rather than individual permissions, making it easy to adjust when an employee’s role changes.
- Constraints: Constraints add another layer of security by enforcing limits on roles and user actions. Examples include time-based access or access limited to certain IP addresses, adding flexibility and control to ensure only the right users can access resources under the right conditions.
A. Benefits of RBAC
- Stronger Security: Ensures users access only what they need, reducing insider and outsider threats.
- Easier Compliance: Aligns with standards like HIPAA, SOX, and GDPR through consistent access policies.
- Faster Onboarding/Offboarding: Automates access changes based on roles, saving IT time.
- Centralized Access Control: Provides clear visibility into who has access to what and why.
- Scalable Access Management: Easily supports growing teams and new apps without added complexity.
3. Access control list (ACL) vs RBAC: Key differences for modern IT
Selecting the right access control model requires evaluating scale, audit requirements, and how dynamically permissions must change:
- Access Control Lists (ACL): Attaches permissions directly to resources; simple for small environments but difficult to manage in complex enterprise settings.
- Attribute-Based Access Control (ABAC): Enables context-aware, dynamic policies based on factors like device and location, though at a high governance cost.
- Relationship-Based Access Control (ReBAC): Manages access through ownership and sharing graphs, ideal for collaboration but difficult to audit.
- Role-Based Access Control (RBAC): The pragmatic standard for IT and security teams, providing structured permissions and audit trails that map clearly to compliance.
4. How to Implement RBAC Without Chaos?
Successfully implementing RBAC requires a clear strategy. Here’s a step-by-step approach to deploying RBAC in your organization:
A. Defines roles and permissions:
Identify key roles and the specific permissions each requires. Consult department leaders to determine access needs for each job function and avoid creating too many overlapping roles.
B. Assign users to roles:
Assign users based on their responsibilities after defining roles. For example, an IT admin would have different permissions than an HR specialist, ensuring each user has access only to what they need.
C. Add role-based limits:
Use constraints to control actions or data access based on time, location, or network. These controls strengthen security by guarding against unauthorized access.
D. Review access regularly:
Regularly audit roles and permissions to ensure appropriate access as roles shift or employees leave. Ongoing monitoring helps maintain secure permissions and ensures compliance.
5. Role-based access control role-engineering checklist
Before assigning a single permission, role engineering requires a disciplined baseline. Use this checklist to structure your role-based access control implementation from the ground up:
- Inventory all apps and data assets: Catalog every SaaS tool, internal system, and sensitive dataset that requires access control.
- Identify role owners: Assign a named owner, such as a team lead or department head, who is accountable for each role’s permission set.
- Map least-privilege permissions: Document only the minimum access required for each role and cross-reference it against your access control list entries.
- Define constraints: Apply separation of duties where conflicting permissions exist and configure just-in-time or time-based access for elevated or temporary privileges.
- Document exceptions formally: Log every out-of-role access grant with a business justification, approver, and expiration date.
- Set a review cadence: Schedule quarterly role reviews as a recurring audit checkpoint to prevent permission drift.
6. Still Managing Access Manually? Meet RBAC Tools.
- Automated Lifecycle Management: Operationalizes role-based access control by automating provisioning and deprovisioning as employees join, move, or exit the organization.
- Seamless Integration: Connects bidirectionally with your Identity Provider (IdP), HRIS, and procurement workflows to sync permissions in real time.
- Continuous Monitoring: Actively discovers access levels and identifies permission drift to ensure user rights always align with defined role boundaries.
- Audit-Ready Compliance: Generates tamper-evident audit trails and automated evidence, transforming months-long reviews into efficient, continuous cycles.
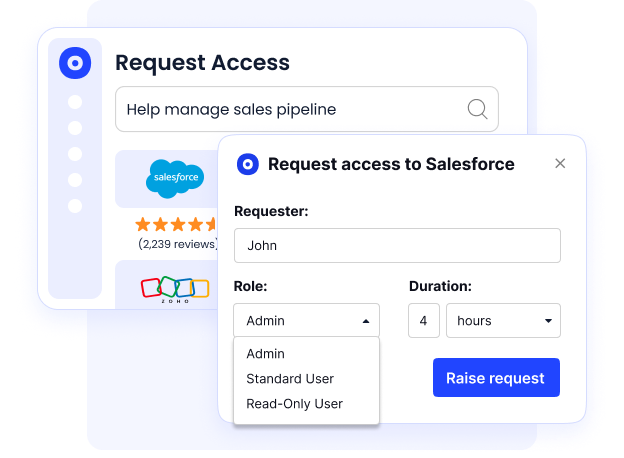
- Just-in-Time Access: Supports time-limited, elevated access via ticketing systems to maintain security without interrupting existing workflows.
- Enhanced Visibility: Provides IT and security teams with meaningful control and visibility, making role-based access control implementation a living process rather than a one-time project.
7. What to Look for in an RBAC Tool Before You Regret It?
RBAC tools vary in effectiveness. Prioritize solutions that reduce IT workload and deliver concrete operational results rather than just surface-level features.
Effective tools track feature-level usage to distinguish active users from idle license holders.
Use this checklist to align procurement and security teams during vendor evaluation:
- Fast onboarding and discovery: Visibility into roles, permissions, and SaaS access within days.
- Bi-directional integrations: Native two-way sync with Okta, Jira, Coupa, and HRIS systems.
- Automated JIT access and deprovisioning: Time-bound access with instant offboarding triggers.
- Auditor-ready evidence: Automated access reviews with deprovisioning proof.
- Granular usage intelligence: Feature-level activity insights beyond login data.
- No-code workflow automation: Configurable provisioning and review workflows inside tools like Slack.
8. How does CloudEagle.ai make RBAC easier?
Implementing Role-Based Access Control (RBAC) can be overwhelming, especially for growing organizations with evolving roles and permissions.
CloudEagle.ai streamlines this process by offering powerful, automated tools to simplify RBAC management, reduce administrative workload, and maintain high-security standards.
Here’s how CloudEagle.ai can make your RBAC implementation seamless and effective:
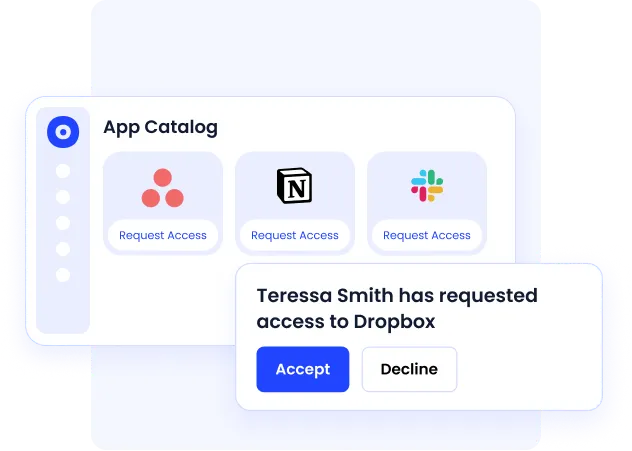
A. Centralized SaaS Management with Access Control
Managing access across multiple SaaS applications can be complex due to tool sprawl. CloudEagle.ai simplifies this with a centralized SaaS management platform that streamlines role-based access control from a single dashboard.
This centralized system allows IT teams to manage and revoke permissions efficiently without logging into each application individually. It ensures secure, appropriate access across all tools while saving time and reducing the risk of security gaps.
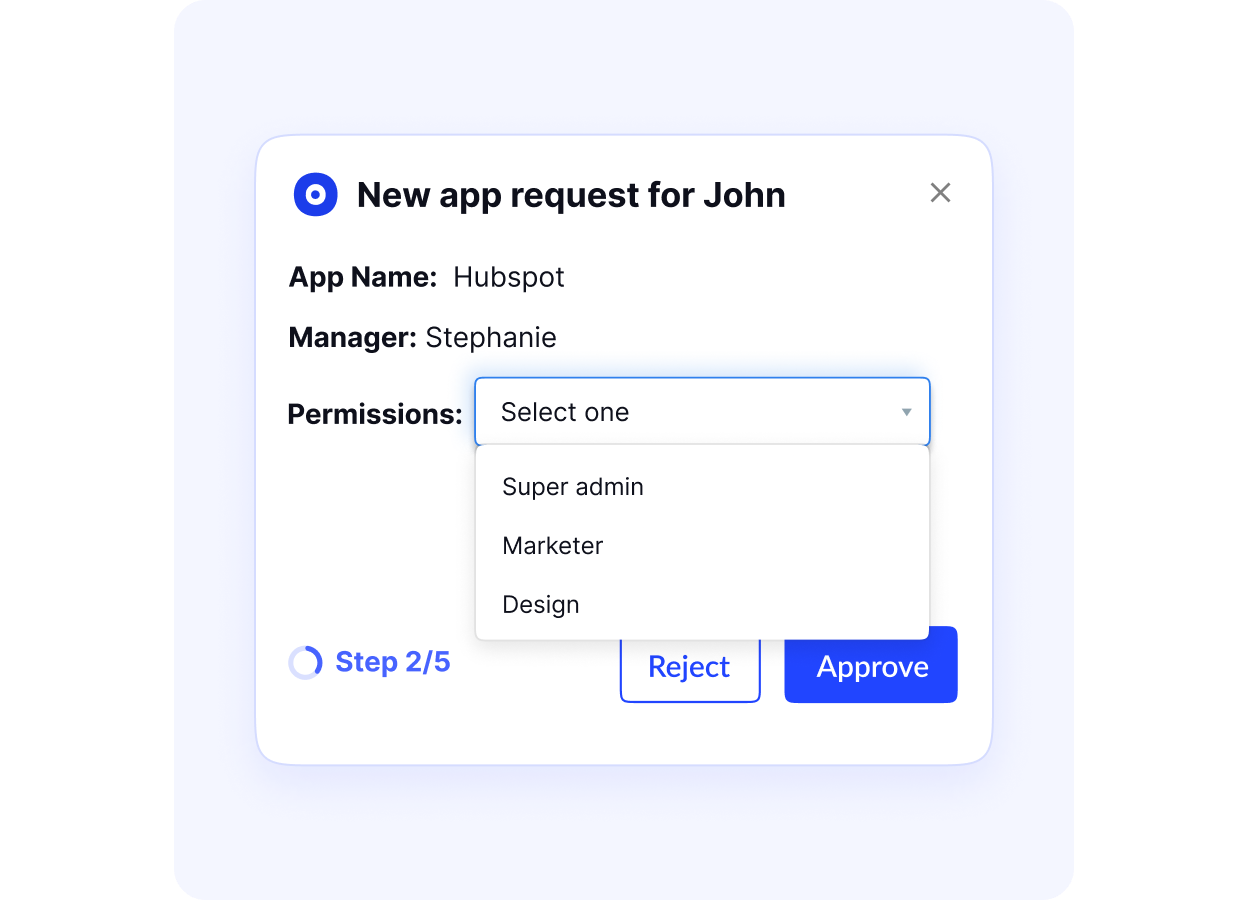
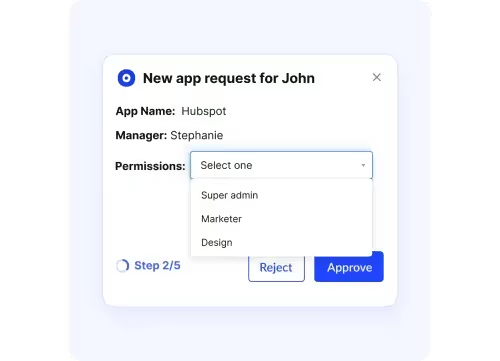
B. Automated User Provisioning and Deprovisioning Process
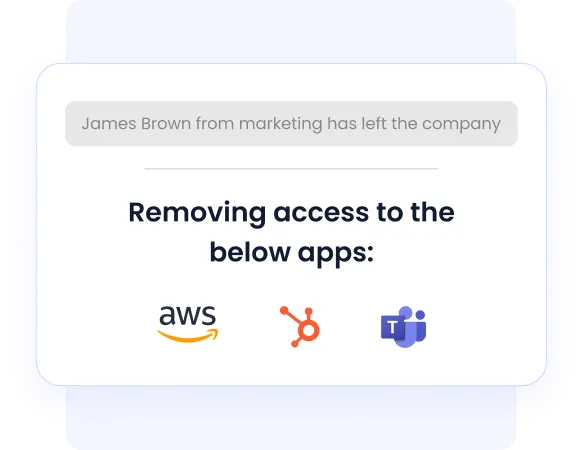
Manual provisioning is slow and increases SaaS compliance risks. CloudEagle.ai automates this by assigning roles when users join and instantly deactivating access when they leave.
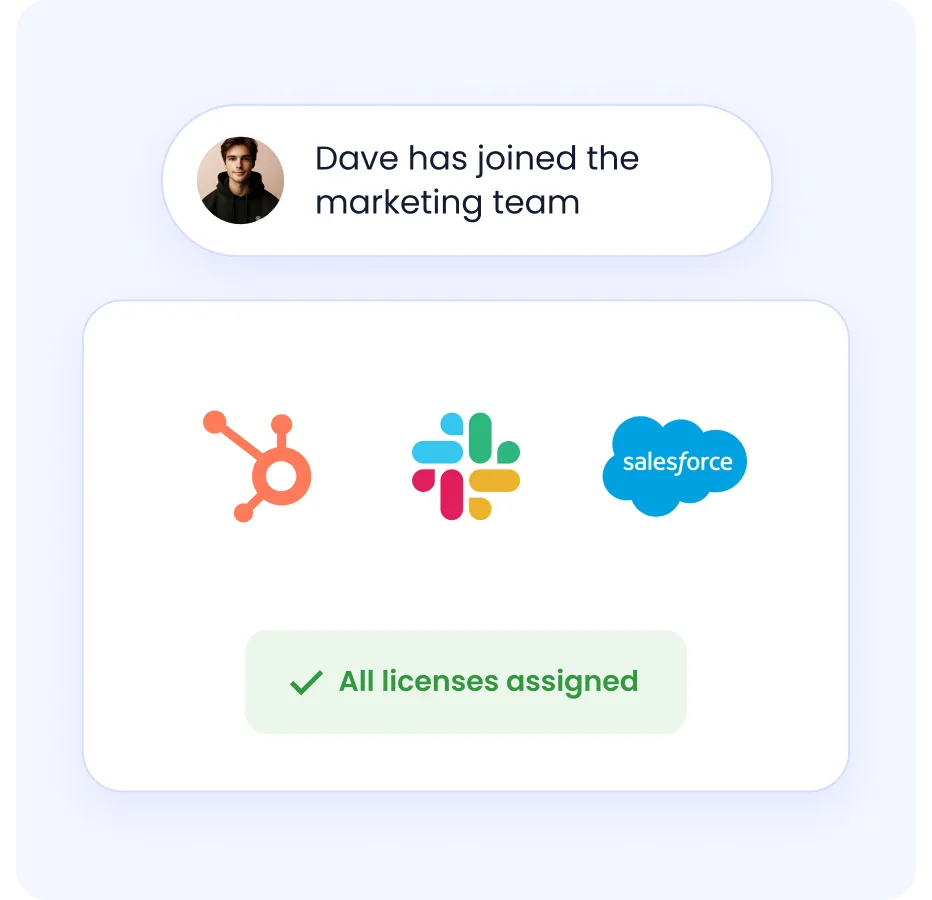
This end-to-end automation saves time and ensures security permissions remain current.
C. Ensuring Compliance with Security and Access Reviews
CloudEagle.ai simplifies compliance and security audits by automating access reviews and reports.
These schedules ensure alignment with industry regulations like GDPR, HIPAA, and SOX while identifying outdated permissions proactively.
D. Automate app access reviews for audits
Meeting SOC2 and ISO 27001 standards requires regular reviews.
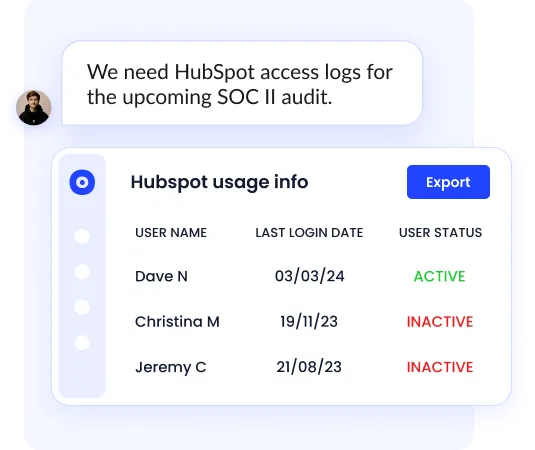
CloudEagle.ai automates this process, providing audit trails and proof of deprovisioning on a single dashboard, eliminating the need for manual app logins.
E. Manage and monitor privileged access
Unmanaged privileged access creates security risks.
CloudEagle.ai automatically manages access levels for high-stakes systems like AWS and NetSuite, protecting sensitive environments from unauthorized activity.
F. Integrating RBAC with Slack and Other Collaboration Tools
CloudEagle.ai extends RBAC to Slack, Microsoft Teams, and Zoom. It automatically adjusts access to channels and shared resources based on role changes.
This integration secures sensitive information while enhancing team productivity through automated provisioning.
9. Top 5 Role Based Access Control Best Practices for IT Security
Implementing RBAC can be complex, especially as organizations scale and user roles diversify. Even a well-intentioned RBAC system can lead to excessive administrative burden, security gaps, and compliance issues without careful planning.
Here’s a closer look at the common challenges in RBAC implementation and best practices to tackle them effectively:
A. Define standard roles organization-wide
A common challenge in RBAC systems is role explosion, which occurs when too many roles are created to meet granular access needs, leading to a complex and confusing structure.
For instance, if every department has unique roles with slight variations, managing access becomes overwhelming.
To prevent this, start by defining core roles that capture broad access levels, like"Manager"or "Team Member", then refine only where necessary.
Pro Tip: Use a role-mapping tool like CloudEagle.ai to analyze and consolidate roles with overlapping permissions. A well-designed RBAC system often has 20-30% fewer roles after consolidation, saving time and reducing risk.
B. Follow the Principle of Least Privilege (PoLP)
Assign users only the minimum level of access required to perform their job duties. Avoid giving full access by default — instead, tailor roles to include only necessary permissions.
Why it matters: Reduces the risk of data breaches and unauthorized activities due to over-permissioned accounts.
C. Automate Role Assignment and Deprovisioning
Use RBAC-enabled tools or identity management platforms to automate user provisioning, role changes, and offboarding.
When an employee changes departments or leaves the company, their access should be adjusted or revoked immediately.
Use RBAC-enabled tools or identity management platforms to automate user provisioning, role changes, and offboarding. When an employee changes departments or leaves the company, their access should be adjusted or revoked immediately.
Why it matters: Eliminates manual errors, speeds up onboarding, and ensures compliance with access control policies.
D. Onboarding and Training:
For RBAC to work smoothly, employees need to understand the boundaries of their permissions. Clear onboarding and regular training sessions help employees navigate their access privileges and reduce the risk of accidental policy breaches.
For example, finance team members might need guidance on accessing certain financial records without modifying them. To improve user adoption, create role-specific training materials and quick-reference guides.
Pro Tip: Use interactive provisioning software, such as role-based learning modules or in-app guidance systems, to make training hands-on and engaging.
E. Conduct Regular Access Audits and Role Reviews
Schedule quarterly or biannual audits to review user-role assignments, identify over-privileged users, and adjust outdated roles. Tools like CloudEagle.ai can automate these reviews with audit trails and alerts.
Why it matters: Maintains up-to-date access policies, reduces risk, and supports audit readiness for frameworks like SOC 2 and ISO 27001.
F. Map Roles to Compliance Requirements
Align each role and its permissions with compliance needs (HIPAA, GDPR, SOX, etc.). Include access monitoring and documentation as part of your compliance workflows.
Why it matters: Ensures you’re audit-ready and reduces the risk of regulatory penalties due to improper access controls.
10. How to Standardize RBAC Models
Choosing the right role based access control model depends on your organization’s risk profile and operational pace:
- Core RBAC: Ideal for agile, fast-growing teams. It provides a direct path to least privilege and is easy to audit, though it requires active management to prevent over-permissioning as headcount scales.
- Hierarchical RBAC: Best for organizations with structured reporting. Senior roles inherit permissions from junior ones, reducing IT duplication and streamlining compliance reviews for SOC 2 or ISO 27001.
- Constrained RBAC: The standard for regulated industries like finance and healthcare. It enforces separation of duties (SoD) to prevent fraud and ensures compliance with strict SOX or HIPAA audit requirements.
11. What Firms Should Know About Role-Based & Permission-Based Access Controls?
Role-based access control (RBAC) groups permissions by job function, streamlining management at scale. One update to a role modifies access for all assigned users, reducing manual effort.
In contrast, individual permission grants offer granularity but increase operational overhead.
This often leads to permission sprawl, where clear visibility into access rights is lost. Each approach presents different tradeoffs for stakeholders:
- CISOs need least-privilege enforcement and audit-ready evidence. RBAC delivers both through structured role definitions and consistent access reviews; permission-based systems make this harder to prove during audits.
- IT teams care about MTTR for access requests. Role-based models reduce ticket volume by enabling faster provisioning. Assigning a role is one action versus configuring individual permissions across multiple systems.
- Executives face risk and ROI exposure. Permission drift in ungoverned environments increases breach surface area and compliance penalties, directly affecting the bottom line.
Exception management is the primary risk in access control. Temporary privileges frequently become permanent without strict oversight. Organizations must implement time-bound access and assign owners to review exceptions.
This layer of ownership prevents over-privileged accounts and audit gaps within role-based systems.
12. Why RBAC is Essential for Modern IT Security?
In today’s complex IT environment, employees, contractors, and vendors frequently access sensitive data. Here’s why RBAC is essential for protecting data and maintaining control over access:
A. Enhances data protection:
RBAC prevents unauthorized access by limiting permissions based on roles, which protects sensitive information from potential misuse.
B. Simplifies regulatory compliance:
Industries like healthcare, finance, and government adhere to strict compliance standards like HIPAA and SOX. RBAC applies structured access control policies that make meeting these requirements easier.
C. Saves time and costs:
RBAC reduces the need to manage permissions individually, easing the administrative burden. Organizations save time and resources by automating access through roles, allowing IT teams to focus on more strategic initiatives.
13. What are some Common Roles and Examples of RBAC?
RBAC roles follow a consistent logic across every department: grant only what the role requires, and constrain everything else. The table below maps common role-based access control roles to their typical permissions and key constraints, highlighting both privileged and read-only access patterns.
Simplify Access Control with CloudEagle.ai
Understanding and implementing Role-Based Access Control (RBAC) is a huge step toward securing your organization’s data and streamlining operations.
With RBAC in place, you’ve gained a practical, scalable framework that helps keep sensitive information safe, ensures compliance, and minimizes the time spent managing access permissions.
With CloudEagle.ai, RBAC management becomes even easier. Its automated user provisioning, centralized controls, and real-time auditing features allow you to manage access seamlessly across all your SaaS tools.
CloudEagle.ai helps you build a secure, efficient RBAC system tailored to your organization’s needs—so you can stay focused on what matters most.
Book a demo today to know how we can ease your access control system in no time.
FAQs
1. What are the three types of RBAC?
Core RBAC assigns static roles; Hierarchical RBAC allows role inheritance; and Constrained RBAC enforces restrictions like separation of duties. Each model offers a different level of control and flexibility in managing user permissions.
2. What is a real-life example of RBAC?
In HR systems, only recruiters can access applicant data, while payroll staff see compensation details. This role-based segmentation ensures sensitive information is only visible to users who need it for their job.
3. What’s the difference between role-based and permission-based access control?
Role-based access groups permissions by job roles, simplifying access management. Permission-based access assigns rights to users individually, offering more granularity but requiring more manual oversight.
4. How do role-based access control systems support compliance?
RBAC supports compliance by restricting data access, automating access reviews, and providing audit logs. This helps organizations meet regulations like HIPAA, SOC 2, and GDPR while minimizing risk and human error.
5. How does RBAC support Zero Trust security frameworks?
Role-Based Access Control (RBAC) aligns with Zero Trust by enforcing least privilege access. It ensures users only get the minimum permissions required for their roles, reducing lateral movement risks within your systems and enhancing overall security posture.
.avif)
%201.svg)









.avif)




.avif)
.avif)




.png)





